Reentrancy Attack
Learn what a reentrancy attack is and why it remains a critical smart contract risk.
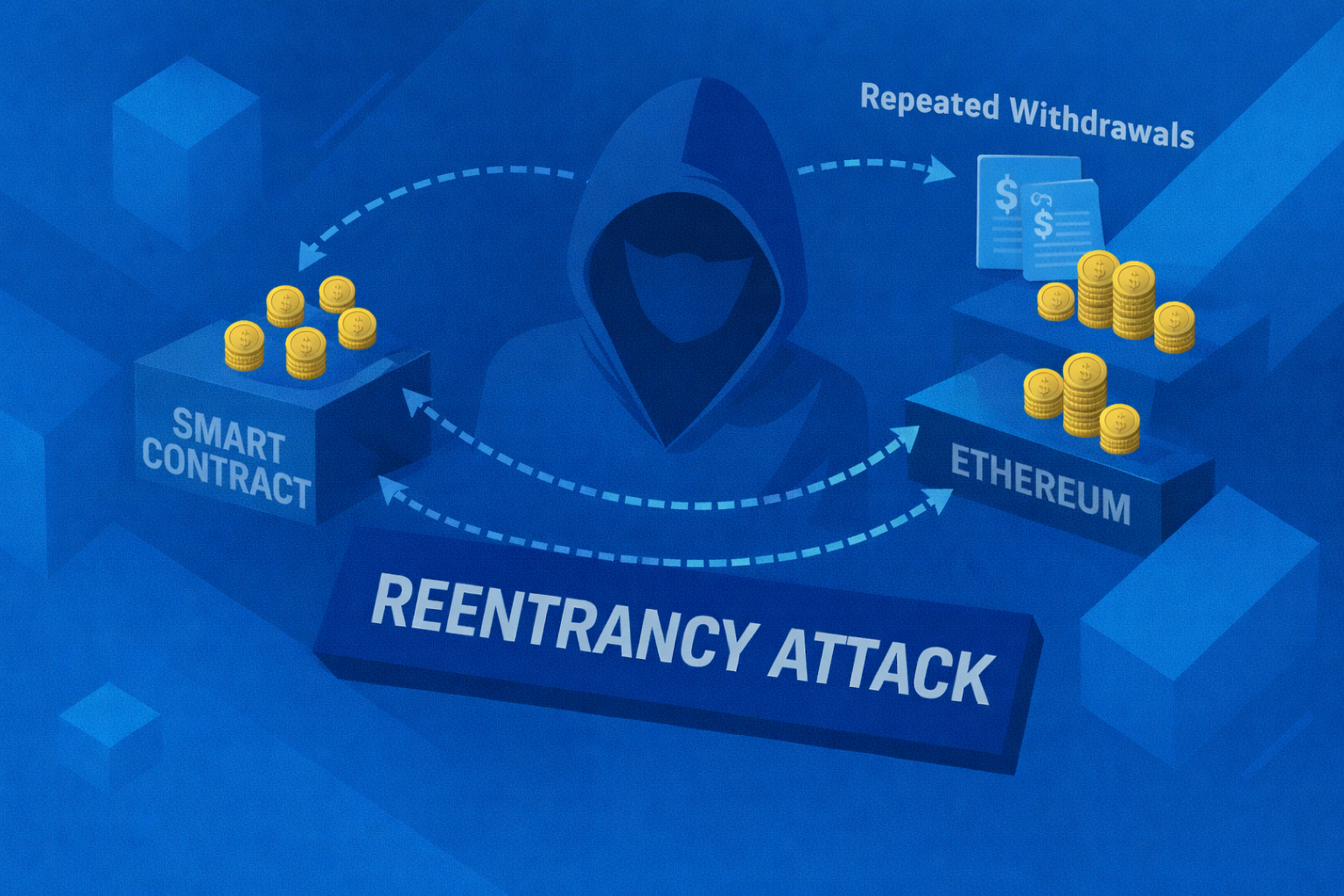
What Is a Reentrancy Attack?
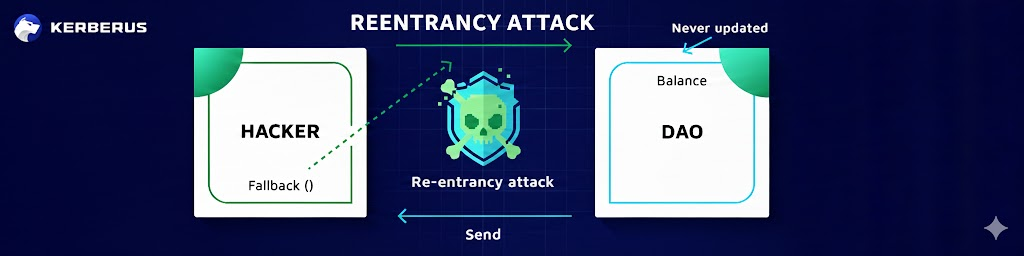
A reentrancy attack is a smart contract exploit where an external call allows a malicious contract to repeatedly re-enter a vulnerable function before state changes are finalized, enabling unauthorized withdrawals.
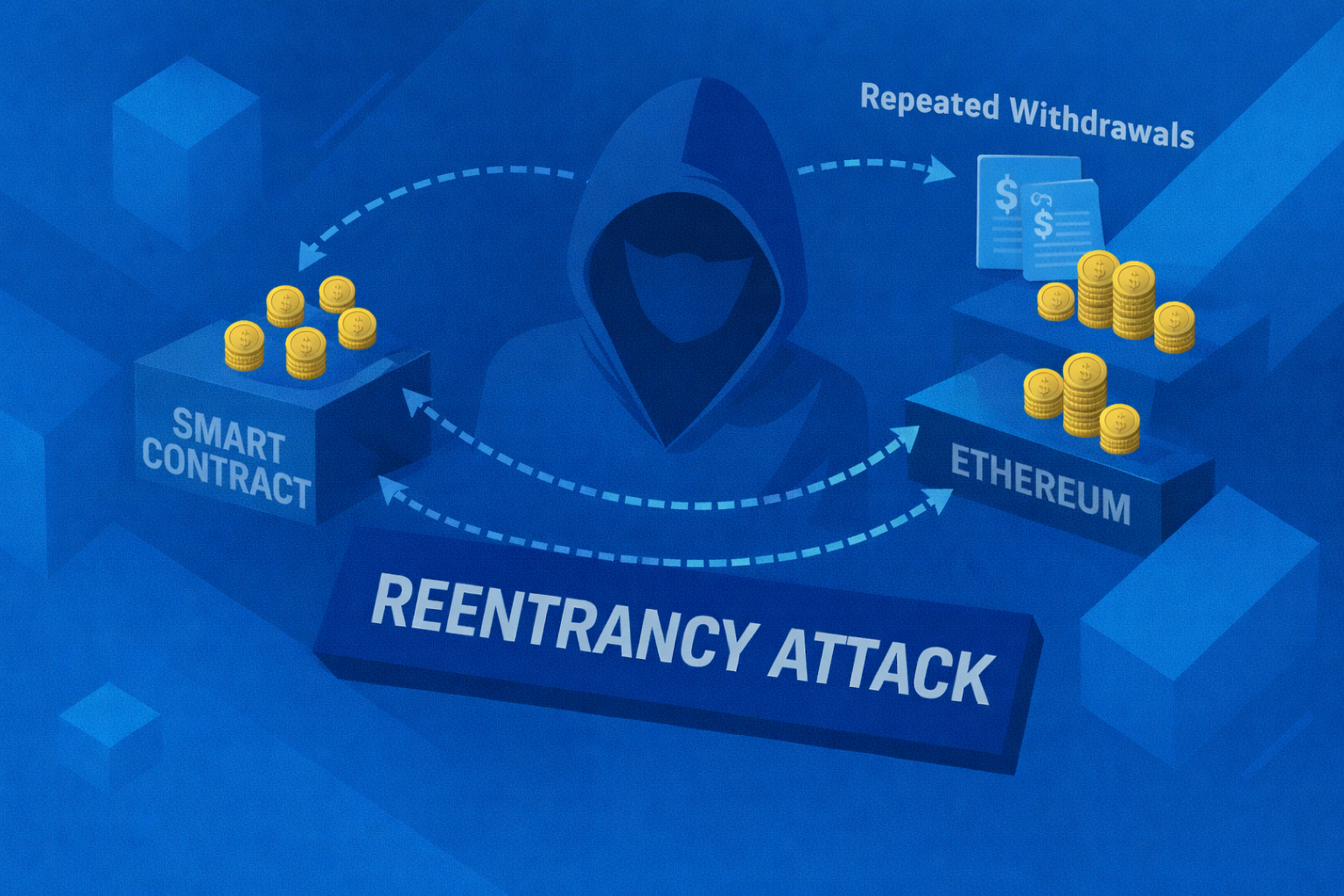
How It Works
If a contract sends funds before updating balances, an attacker can recursively (repeating its own output) call the function to drain assets. This vulnerability famously caused early DeFi losses (see the Ethereum DAO hack) and still remains relevant today.
Reentrancy is a classic smart contract vulnerability that often combines with flash loan attacks to amplify damage. While well-known, it still appears in unaudited or poorly designed contracts.
How to Protect Yourself
- Developers should follow checks-effects-interactions patterns
- Users should favor audited protocols
- Avoid interacting with unknown contracts offering unusually high yields
- Use Kerberus for real-time transaction analysis
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Terms
See more glossary termsInstall once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.