Sybil Attack
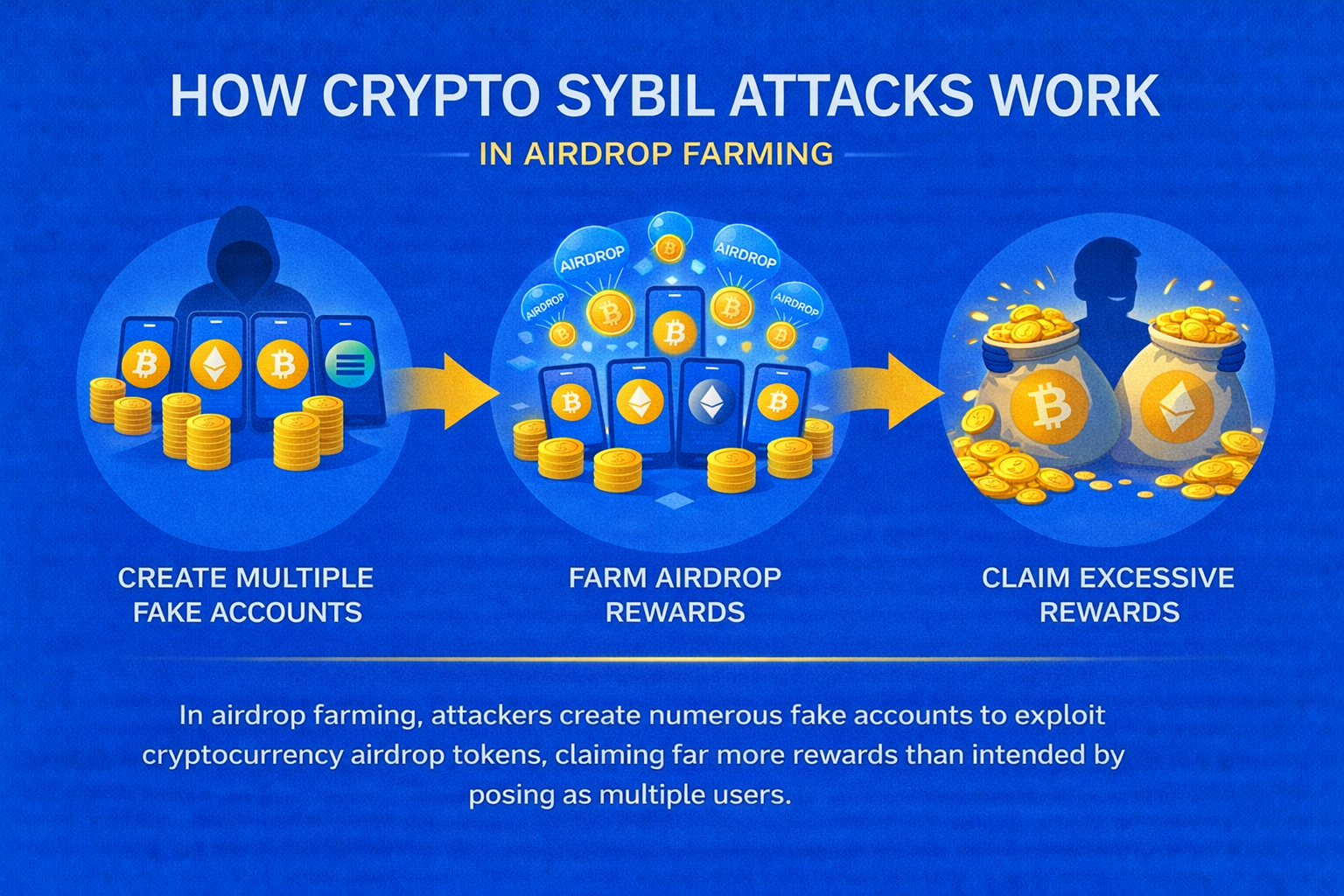
A Sybil attack is when a single entity creates multiple fake identities to gain disproportionate influence over a decentralized network.

What Is a Sybil Attack?
A Sybil attack is a security threat where a single entity creates multiple fake identities or accounts to gain disproportionate influence over a decentralized network, potentially manipulating consensus mechanisms, governance decisions, or economic incentives designed to rely on independent participants.
Named after the book “Sybil” about multiple personality disorder, these attacks exploit systems that assume each participant represents a unique individual or entity with legitimate interests in the network’s success.
Sybils are especially popular to farm airdrops, and as a result, the majority of new crypto projects implement anti-sybil technology to make sure that their launches are not sabotaged by unfair bot and user activity.

How It Works
Attackers create numerous fake accounts, validator nodes, or wallet addresses to appear as multiple independent users. They then use these to vote in governance proposals, manipulate reputation systems, overwhelm network resources, or exploit airdrop distributions and reward mechanisms.
Their playbook usually looks like this:
- Identify an airdrop with weak or unclear Sybil defenses
- Generate many wallet addresses, often in batches
- Acquire “starter” funds to pay gas and look legitimate
- Perform the required actions on each wallet: swaps, bridging, staking, votes
- Mimic human behavior, vary timing, amounts, and routes
- Link wallets through private relays or split funding paths to reduce clustering
- Wait for snapshot and eligibility rules to finalize
- Claim from each wallet, then consolidate tokens to a main wallet and exit
In proof-of-stake networks, attackers might split their stake across multiple validators to appear more decentralized, while in governance tokens, they could create multiple wallets to bypass voting limits or qualification requirements.
How to Protect Yourself
- Protocols can use stake-weighted voting mechanisms that make Sybil attacks economically expensive
- Implement identity verification systems requiring proof of unique personhood
- Monitor for suspicious patterns like coordinated voting or similar transaction histories
The governance attacks on various DeFi protocols where entities acquired tokens across multiple addresses to manipulate proposal outcomes, including attempts to drain protocol treasuries through coordinated voting, demonstrate how Sybil attacks remain a persistent threat to decentralized governance systems.
Written by:
Werner Vermaak is a Web3 author and crypto journalist with a strong interest in cybersecurity, DeFi, and emerging blockchain infrastructure. With more than eight years of industry experience creating over 1000 educational articles for leading Web3 teams, he produces clear, accurate, and actionable organic material for crypto users.
- •8+ years in crypto & blockchain journalism
- •1000+ educational articles for leading Web3 teams
- •Former content lead at CoinMarketCap, Bybit, OKX
Related Terms
See more glossary termsInstall once & immediately get protected from scams, phishing and hacks. Zero losses for 250k+ users in 3 years. Now with up to $30,000 in coverage.